The COVID-19 pandemic has created internal and external challenges in the last couple of years, whether you’re a small mom-and-pop operation or a large corporation that employs hundreds or thousands of employees.
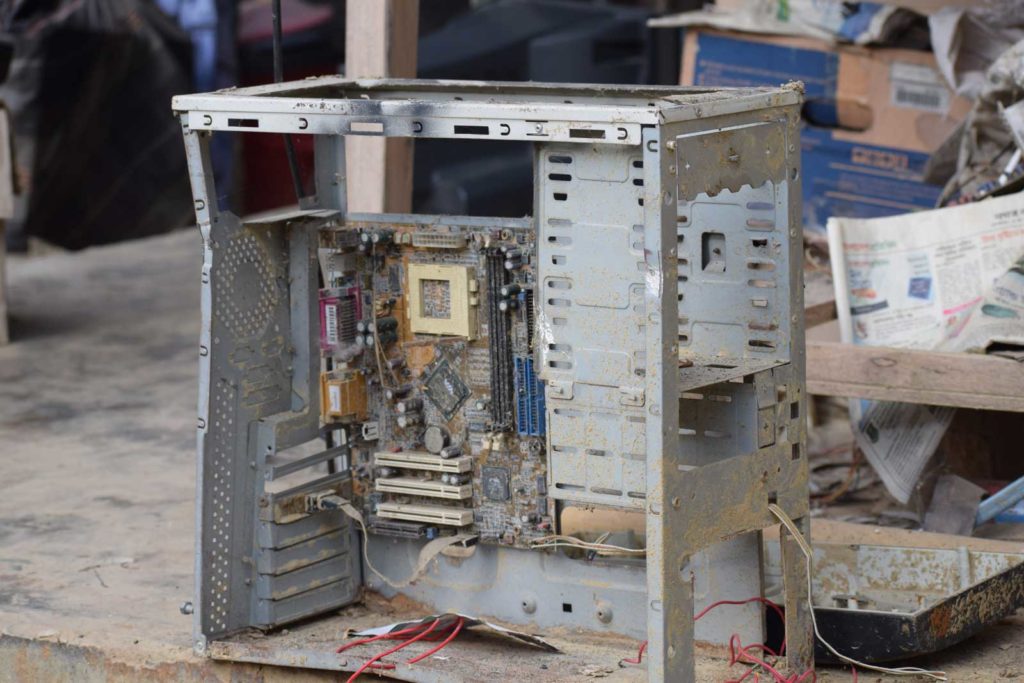
Unfortunately, cybercriminals have upped their games during the pandemic. That means your business is more threatened than ever before by hackers and other types of criminals. By extension, that means your old hard drives and data storage devices could be a weak spot that could be exploited.
As we slowly emerge from the pandemic, if as a business owner you have been lax in maintaining your information security processes and procedures it may be time to revisit the state of your data storage devices.
Here are some things to consider so that a data breach does not victimize your business coming out of the pandemic.
Why data device destruction is so important
The first and most obvious reason why securely destroying old data devices is so important is that you MUST protect yourself, your clients, vendors, employees, and others from any breach of sensitive data.
Whether you are an individual, small business owner, or large business owner, you have a sacred obligation to maintain confidentiality. Identity theft, fraud, embezzlement, and other white-collar crimes can ruin a victim’s life. And in many cases, that victim could be you!
That means if you were on top of it before, you need to redouble your efforts and educate yourself on what has changed since the pandemic started.
Aside from the ethical considerations, are you aware as a business owner that you are required to comply with privacy laws on how to dispose of data storage devices securely? If not, you could face penalties.
Some industries also face higher degrees of regulation due to HIPAA and FACTA laws already on the books. If you’re not well versed in privacy laws, it might be in your best interest to find an expert such as an attorney, document shredding company, or data destruction company who can safely guide you through compliance issues and regulations.
There is also a bottom-line reason for paying attention to appropriate data device destruction. When you leave yourself exposed and suffer a breach, it could threaten the very existence of your business. Not exactly the type of thing you want to hear if you fought through pandemic challenges.
Aside from hacked account theft, customers could also sue or abandon you. Partners and vendors may no longer trust you and may refuse to work with you. Key employees could move on. Your reputation could be tarnished and have a significant impact on landing future customers.
Best practices and a zero-trust security strategy
Don’t think for a minute when your laptops, desktops, cell phones, and other electronics reach the end of their useful service lives that you can take a hammer to them and be done with your data device security efforts.
There are a lot of firms that exist to make sure your data devices are disposed of properly. Business compliance is a critical reason to hire a firm that specializes in data device destruction. Although laws and rules can be inconsistent, all businesses should adopt a “zero-trust security strategy.”
“It’s a concept that basically says, ‘You know what? You can’t trust anybody. You can’t trust people on the outside or the inside,’” according to Gregory Touhill, former deputy assistant secretary of cybersecurity and communications at the U.S. Department of Homeland Security.
This means following best practices instead of just doing enough be meet compliance standards.
Environmental issues are also in play when you contract with a device destruction firm. Instead of just tossing a device in the trash and creating unnecessary e-waste after it has been wiped clean, about 98% of what remains can be recycled.
How data destruction takes place
There are several methods of data destruction for both information and devices:
Delete or reformat – Contrary to what many business owners think, deleting or reformatting files from an electronic device may remove information from a folder, but it doesn’t destroy the data. It’s still on the hard drive or the memory chip. Several online tools can still extract information from a device even after it is reformatted.
Data wiping – You can overwrite data from an electronic device so it can’t be read anymore. There are wiping devices in the marketplace to help you do this. The good news is you can reuse the media after wiping takes place. But the downside is that wiping can take a long time and generally isn’t practical for a large-scale data destruction activity.
Overwriting data – This is a form of data wiping, but it may take several attempts before data is completely cleared from a device. Overwriting is probably the most common way to destroy data, but it is not foolproof. Although it is complicated, thieves can still access information in some cases.
Erasure – This is another term of overwriting.
Degaussing – Data is destroyed using a high-powered magnet. The magnetic field of a device is disrupted, destroying the data. It’s quick and effective, but it also renders the hard drive useless. It’s not a good option if you want to reuse an electronic device. Also, you’re not able to confirm all data has been destroyed. Because the hard drive no longer works, you can’t check to confirm all data has been destroyed. The only way to confirm is by using an expensive electron microscope, which is often impractical.
Physical destruction – Smashing or incinerating old electronics into small pieces is an effective and efficient way to destroy data. It gives you high assurance of data destruction, but it can be costly and create specific “green compliance” issues.
Shredding – This is the most secure and cost-effective way to destroy data, and it’s an efficient way to go for almost any kind of electronic device. It’s a particularly smart route if you have large amounts of e-data to dispose of and guarantees data destruction since it is reduced to pieces no larger than 2 millimeters.
Choosing the right data device destruction company
Data and device destruction is big business, and there are many companies to choose from that will meet your needs. A few things you should look for in a vendor include:
- Compliance. Ask if they are familiar with NSA and NIST guidelines.
- Chain of custody. What are the company’s protocols to protect against a breach? Do they use tamper-proof containers, secured totes, and locked trucks during transit? Do they have secure and monitored facilities?
- Certificates and documentation. Make sure the company provides certificates of sanitization for all destroyed media data. It should include serial numbers, type of media, and how it was sanitized. Also, verify that documentation will be provided that shows an audit trail and proof of erased data.
- Insurance. Does the company have liability insurance to adequately assume responsibility if there is a data breach or mishap? Also, ask about what kind of security training and background checks employees undergo.
- Process. Get a detailed explanation of exactly how data devices will be destroyed and by what method.
The pandemic may have taken you out of many of your best business practices. So, if you value the sensitive customer data you possess and its impact on your business, find a dependable provider to protect against potential headaches and, worse, liability.
 Don’t Be Fooled: Learn How to Effectively Erase Computer Files
Don’t Be Fooled: Learn How to Effectively Erase Computer Files  Make Sure Your Old Hard Drives are Properly Destroyed: Hard Drive Destruction FAQs
Make Sure Your Old Hard Drives are Properly Destroyed: Hard Drive Destruction FAQs  You’re at Risk for Many Different Kinds of Identity Theft
You’re at Risk for Many Different Kinds of Identity Theft 

